Automated Kubetnernetes runbooks
Photo by Markus Winkler on Unsplash
Introduction
Using runbooks can streamline and improve working with Kubernetes by automating repeatable tasks. Bonus point, we can do this using only open source tools.
Photo by Markus Winkler on Unsplash
Using runbooks can streamline and improve working with Kubernetes by automating repeatable tasks. Bonus point, we can do this using only open source tools.
This article is will be helpful to anyone interested in modern complex software development.
In this article we are going to learn how to automate the provisioning of cloud resources via Crossplane and combine it with GitOps practices.
You will most benefit from this blog if you are a Platform or DevOps Engineer, Infrastructure Architect or Operations Specialist.
If you are new to GitOps, read more about it in my blog GitOps with Kubernetes
Let's set the stage by imagining following context. We are working as a part of a Platform Team in a large organization. Our goal is to help Development Teams to onboard get up to speed with using our Cloud Infrastructure. Here are a few base requirements:
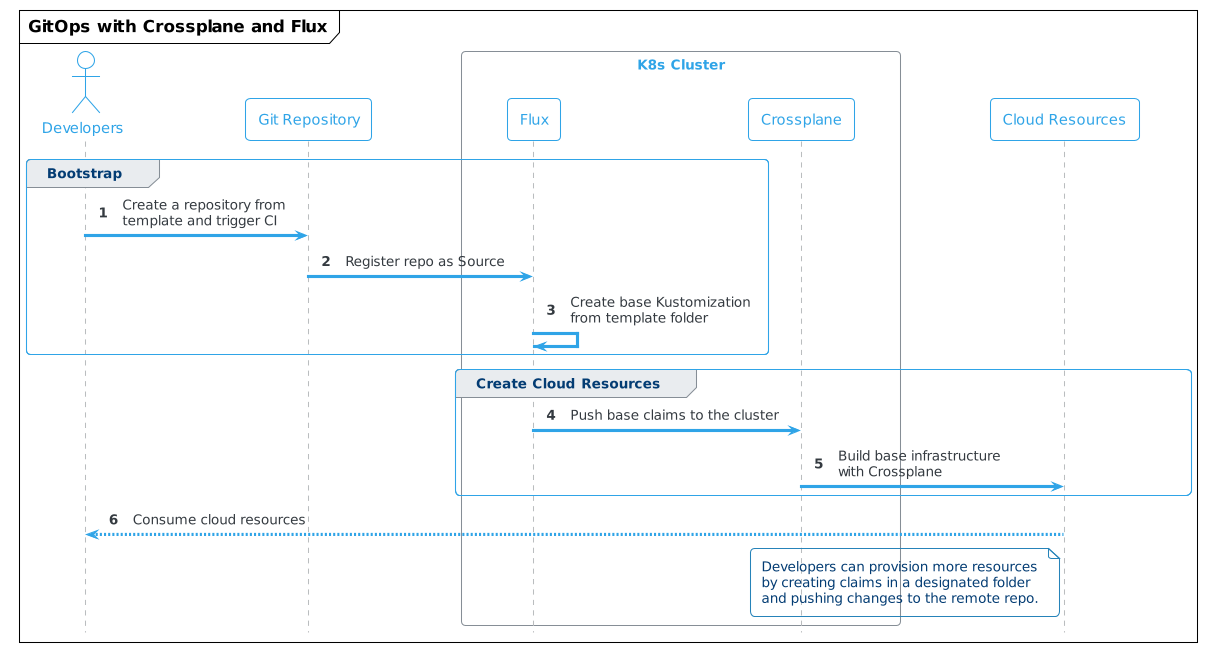
The requirements lead us to an initial architecture proposal with following high level solution strategy.
In real world scenario we would manage Crossplane also using Flux, but for demo purposes we are focusing only on the application level.
The developer experience should be similar to this:
Knowing the requirements and initial architecture, we can start selecting the tools. For our example, the tools we will use are Flux and Crossplane.
We are going to use Flux as a GitOps engine, but the same could be achieved with ArgoCD or Rancher Fleet.
Let's look at the architecture and use cases that both tools support.
Flux exposes several components in the form of Kubernetes CRDs and controllers that help with expressing a workflow with GitOps model. Short description of 3 major components. All those components have their corresponding CRDs.
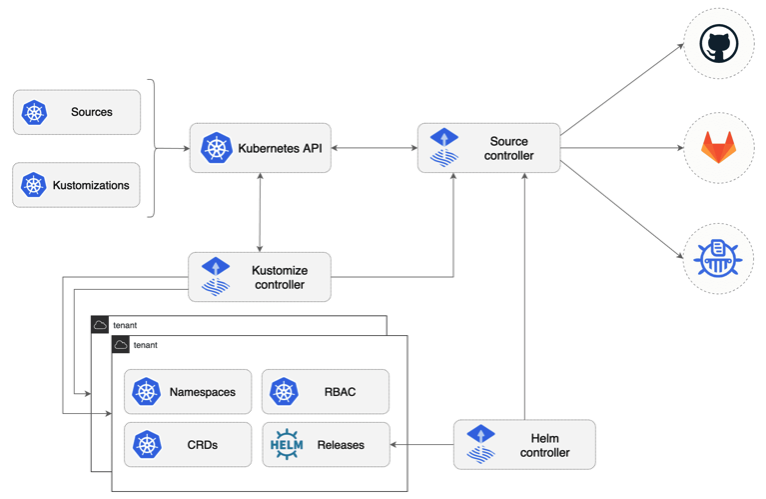 source: https://github.com/fluxcd/flux2
source: https://github.com/fluxcd/flux2
Source Controller Main role is to provide standardized API to manage sources of the Kubernetes deployments; Git and Helm repositories.
apiVersion: source.toolkit.fluxcd.io/v1beta1
kind: GitRepository
metadata:
name: podinfo
namespace: default
spec:
interval: 1m
url: https://github.com/stefanprodan/podinfo
Kustomize Controller This is a CD part of the workflow. Where source controllers specify sources for data, this controller specifies what artifacts to run from a repository.
This controller can work with kustomization files, but also plain Kubernetes manifests
apiVersion: kustomize.toolkit.fluxcd.io/v1beta2
kind: Kustomization
metadata:
name: webapp
namespace: apps
spec:
interval: 5m
path: "./deploy"
sourceRef:
kind: GitRepository
name: webapp
namespace: shared
Helm Controller This operator helps managing Helm chart releases containing Kubernetes manifests and deploy them onto a cluster.
apiVersion: helm.toolkit.fluxcd.io/v2beta1
kind: HelmRelease
metadata:
name: backend
namespace: default
spec:
interval: 5m
chart:
spec:
chart: podinfo
version: ">=4.0.0 <5.0.0"
sourceRef:
kind: HelmRepository
name: podinfo
namespace: default
interval: 1m
upgrade:
remediation:
remediateLastFailure: true
test:
enable: true
values:
service:
grpcService: backend
resources:
requests:
cpu: 100m
memory: 64Mi
Let’s look how the Crossplane component model looks like. A word of warning, if you are new to Kubernetes this might be overwhelming, but there is value in making an effort to understand it. The below diagram shows the Crossplane component model and its basic interactions.
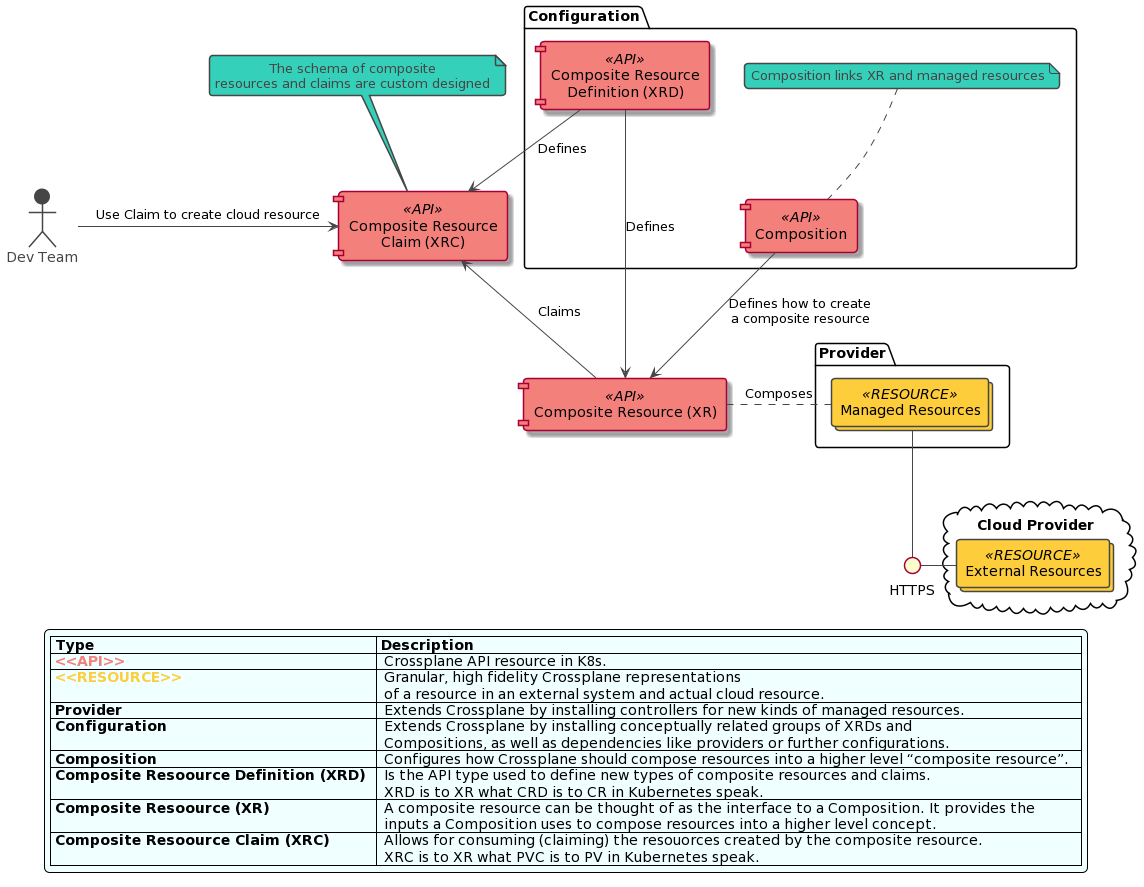 Source: Author based on Crossplane.io
Source: Author based on Crossplane.io
Learn more about Crossplane in my blog "Infrastructure as Code: the next big shift is here"
If you want to follow along with the demo, clone this repository, it contains all the scripts to run the demo code.
In this demo, we are going to show how to use Flux and Crossplane to provision an EC2 instance directly from a new GitHub repository. This simulates a new team on boarding to our Platform.
To follow along, you will need AWS CLI configured on your local machine.
Once you obtain credentials, configure default profile for AWS CLI following this tutorial.
Locally installed you will need:
Run make in the root folder of the project, this will:
If you are running on on Mac, use
make setup_macinstead ofmake.
Following tools need to be installed manually
IMPORTANT: The demo code will create a small EC2 Instance in eu-centra-1 region. The instance and underlying infrastructure will be removed as part of the demo, but please make sure all the resources were successfully removed and in case of any disruptions in the demo flow, be ready to remove the resources manually.
make, this will install Crossplane with AWS provider and configure secret to access selected AWS account
Flux CLI was installed as put of the Makefile scrip, but optionally you can configure shell completion for the CLI
. <(flux completion zsh)Refer to the Flux documentation page for more installation options
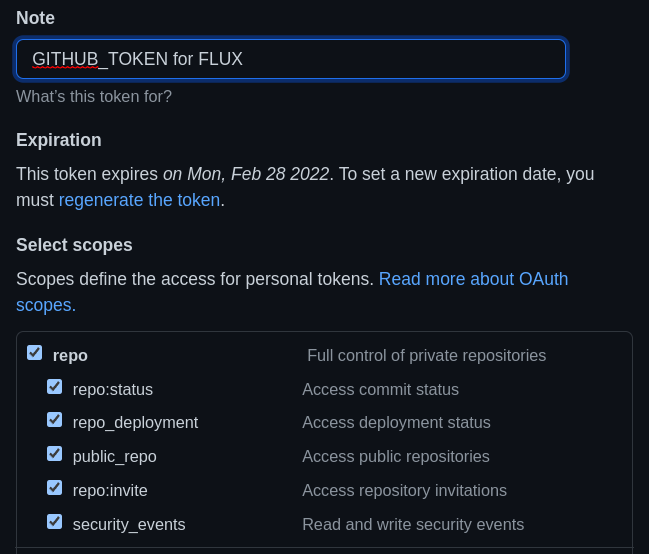
export GITHUB_TOKEN=<token copied form GitHub>export GITHUB_USER=<your user name>Flux will look for GITHUB_USER and GITHUB_TOKEN variables and once found will create a private repository on GitHub where Flux infrastructure will be tracked.
flux bootstrap github \
--owner=${GITHUB_USER} \
--repository=flux-infra \
--path=clusters/crossplane-cluster \
--personal
Now we will install a Crossplane Composition that defines what cloud resources to crate when someone asks for EC2 claim.
setup Crossplane composition and definition for creating EC2 instances
kubectl crossplane install configuration piotrzan/crossplane-ec2-instance:v1fork repository with the EC2 claims
gh repo fork https://github.com/Piotr1215/crossplane-ec2
answer YES when prompted whether to clone the repository
clone the flux infra repository created in your personal repos
git clone git@github.com:${GITHUB_USER}/flux-infra.git
cd flux-infra
add source repository to tell Flux what to observe and synchronize
Flux will register this repository and every 30 seconds check for changes.
execute below command in the flux-infra repository, it will add a Git Source
flux create source git crossplane-demo \
--url=https://github.com/${GITHUB_USER}/crossplane-ec2.git \
--branch=master \
--interval=30s \
--export > clusters/crossplane-cluster/demo-source.yaml
the previous command created a file in clusters/crossplane-cluster sub folder, commit the file
git add .git commit -m "Adding Source Repository"git pushexecute kubectl get gitrepositories.source.toolkit.fluxcd.io -A to see active Git Repositories sources in Flux
setup watch on the AWS managed resources, for now there should be none
watch kubectl get managed
create Flux Kustomization to watch for specific folder in the repository with the Crossplane EC2 claim
flux create kustomization crossplane-demo \
--target-namespace=default \
--source=crossplane-demo \
--path="./ec2-claim" \
--prune=true \
--interval=1m \
--export > clusters/crossplane-cluster/crossplane-demo.yaml
git add .git commit -m "Adding EC2 Instance"git pushafter a minute or so you should see a new EC2 Instance being synchronized with Crossplane and resources in AWS
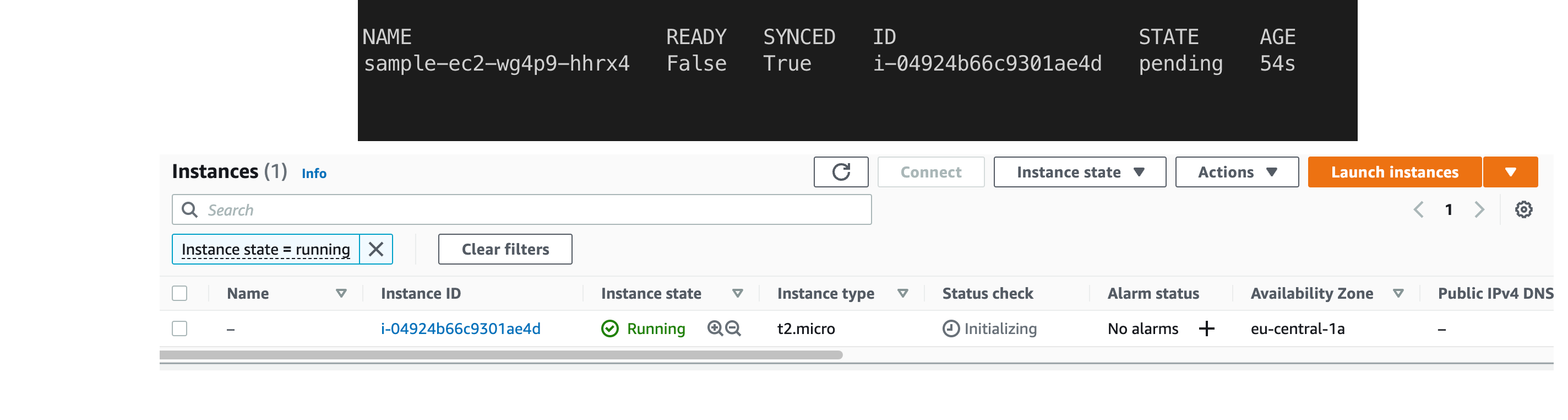
Let's take a step back and make sure we understand all the resources and repositories used.
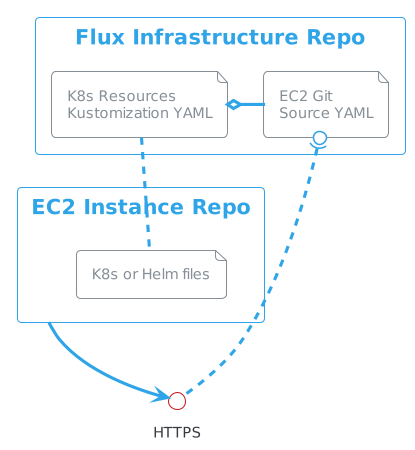
The first repository we have created is what Flux uses to manage itself on the cluster as well as other repositories.
In order to tell Flux about a repository with Crossplane EC2 claims, we have created a GitSource YAML file that points to HTTPS address of the repository with the EC2 claims.
The EC2 claims repository contains a folder where plain Kubernetes manifest files are located. In order to tell Flux what files to observe, we have created a Kustomization and linked it with GitSource via its name. Kustomization points to the folder containing K8s manifests.
rm ec2-claim/claim-aws.yamlgit add .git commit -m "EC2 instance removed"the ec2-claim folder must be present in the repo after the claim yaml is removed, otherwise Flux cannot reconcile
In case you cannot use the repository, it's possible to cleanup the resources by deleting them from flux.
flux delete kustomization crossplane-demo will remove all the resources from the cluster and AWSkubectl delete VirtualMachineInstance sample-ec2watch kubectl get managed output doesn't contain any AWS resourcesmake cleanupflux-infra repositoryGitOps with Flux or Argo CD and Crossplane offers a very powerful and flexible model for Platform builders. In this demo, we have focused on applications side with Kubernetes clusters deployed some other way, either with Crossplane or Fleet or Cluster API etc.
What we achieved on top of using Crossplane’s Resource Model is the fact that we do not interact with kubectl directly any longer to manage resources, but ratter delegate this activity to Flux. Crossplane still runs on the cluster and reconciles all resources. In other words, we've moved the API surface from kubectl to Git.
In this blog, we will look at the evolution of software infrastructure; provisioning, delivery and maintenance.
If you are interested in modern DevOps and SRE practices, this article is for you.
Infrastructure as Code (IaC) is a common pattern where virtualized infrastructure and auxiliary services can be managed using configuration expressed in almost any language, usually hosted in a source code repository.
Every once in a while software industry is shaped by significant events called Paradigm Shift. Here are a few such events that made Infrastructure as Code what it is today:

This documentation assumes basic knowledge of Kubernetes and kubectl. To learn or refresh on container orchestration related concepts, please refer to the official documentation:
 Photo by Antoine Petitteville on Unsplash
Photo by Antoine Petitteville on Unsplash
Docker introduced containers technology as mainstream around 2013. Since then, containerization became an integral part of the cloud and digital transformations. Nowadays most of the traditional server workloads such as web APIs, web apps (broadly speaking server side workloads), are containerized. Heck, even Microsoft saw the writing on the wall and since 2016 windows containers are also there (albeit a bit on the heavy side). 2017 saw the introduction of Kubernetes, a container orchestration, which even more cemented already strong position of containers as compute workhorses.

In 2017, a cloud-native company Weaveworks release a blog post called “GitOps — Operations by Pull Request”. The post introduces the term GitOps defining it as *using Git as a source of truth to operate almost anything. *Since then GitOps movement has been growing and gaining in popularity.